De-Anonymization via Location
Fog Reveal differs from other cellphone tracking technologies (such as Stingrays) in that it relies on IDs associated with online advertising profiles. These IDs are connected across various phone apps that gather details about users’ online habits, which are in turn sold to marketing firms. It’s kind of a side business that a lot of app developers are engaged in, unless the app they offer is free, in which case, you might assume it’s one of their core revenue streams. Essentially, characteristics about your online activities across numerous apps are assigned to these IDs, which are often device specific, and they in turn allow other companies to target you with specific types of ads; the aim being to predict your interests and, hopefully, convince you to spend some money.
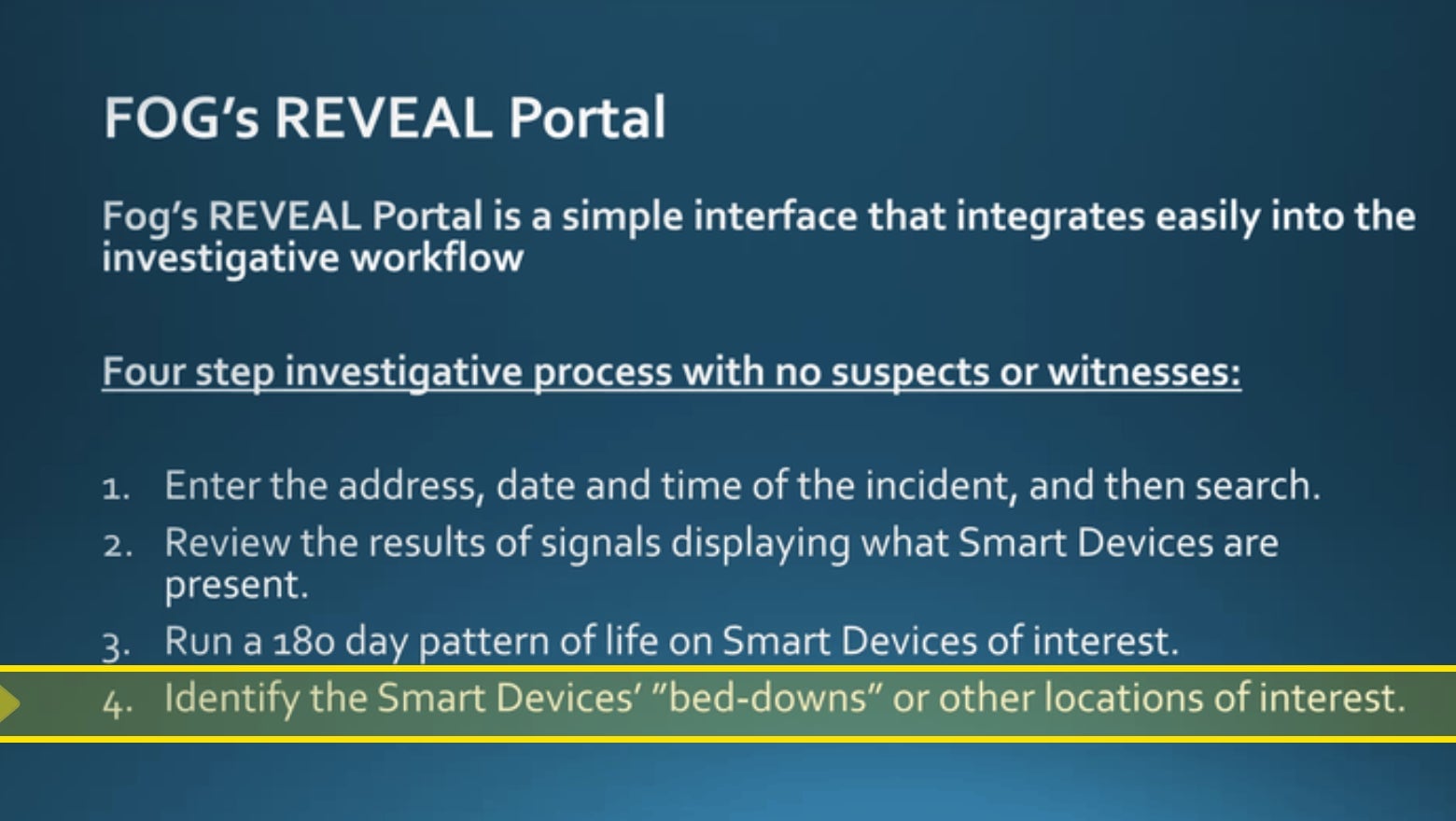
These IDs do not contain your actual name, though it is certainly possible to de-anonymize them by comparing the ID to other datasets that do contain names. And for the purposes of policing, this may be irrelevant anyway. With a thorough list of locations where the device has been present, it’s unlikely it’s difficult for police to discern who they’re tracking. You can imagine: wherever the device rests overnight is probably the user’s home address, and, similarly, wherever it stops for most of the day is likely their place of work.





