A ransomware attack on international IT firm Kaseya appears to have infected hundreds of smaller sized businesses that rely on the company’s product, including many based in the U.S.
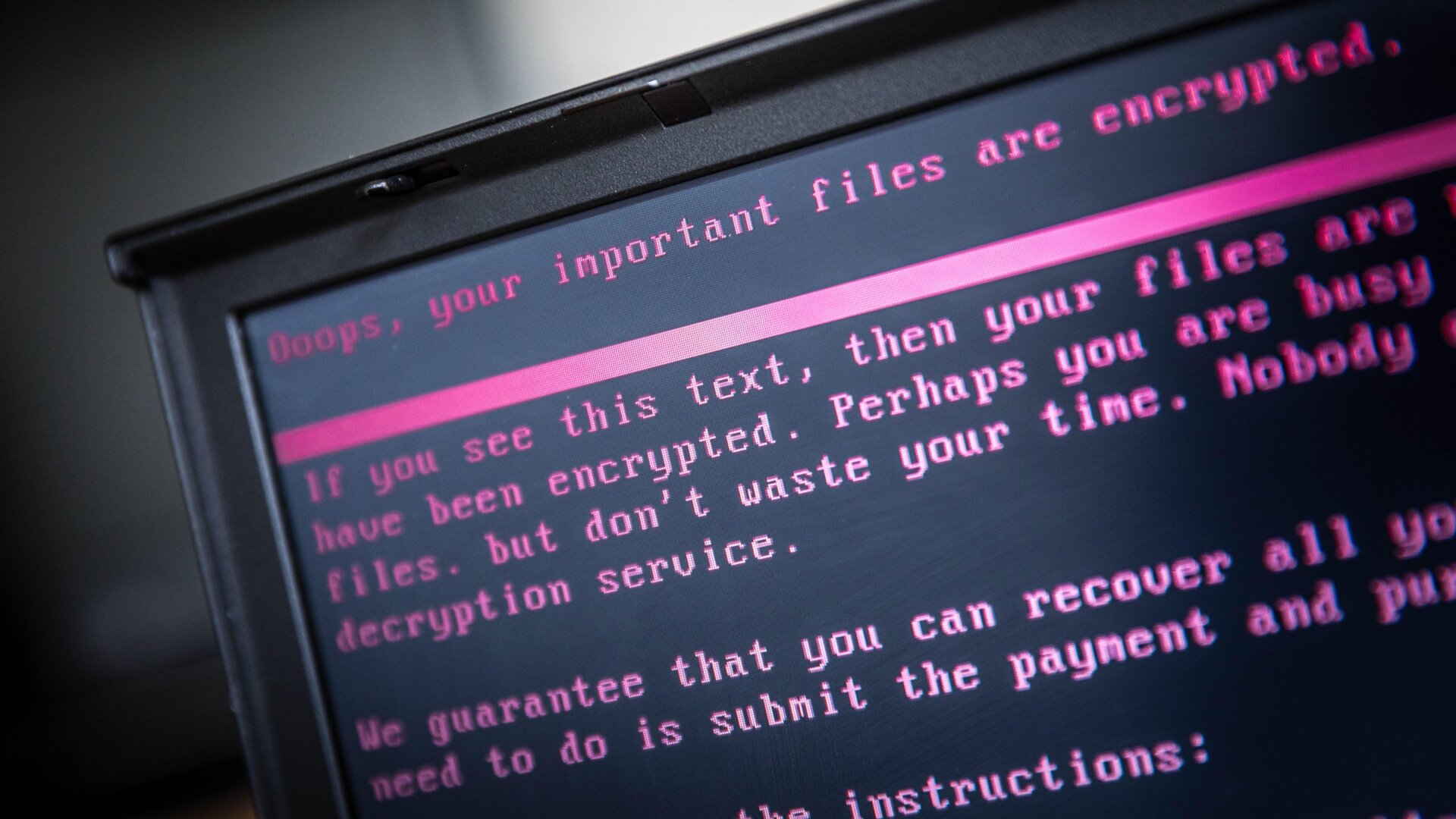
On Friday, Kaseya disclosed that it had been the victim of a “potential attack,” implying that hackers were somehow targeting users of its VSA on-premises product. Customers should shut down VSA “IMMEDIATELY,” an alert reads.
While the company has claimed that the attack is “limited to a small number” of customers, Kaseya’s position in a wider IT ecosystem means the effects of this attack could be quite large—potentially making it one of the largest ransomware attacks in history.
Kaseya sells its products to firms known as managed service providers (MSPs)—companies that provide remote IT services to hundreds of smaller-sized businesses that don’t have the resources to conduct those processes in-house. MSPs use Kaseya’s VSA cloud platform to help manage and send software updates to their clients, as well as to manage other user issues.
However, VSA’s widespread use is exactly what has allowed hackers to exploit it and allegedly infect droves of companies. The Record reports that the ransomware gang responsible for this gargantuan attack is abusing Kaseya’s product by “using a malicious update” to deploy its malware to “companies across the world.” While it’s unclear the exact mechanics of the attack or how and when it occurred, security experts are reporting that the ransomware is affecting not just the MSPs that use VSA, but their clients too. In other words, the ransomware seems to have infected hundreds of smaller-sized businesses that rely on the MSPs for IT support.
Security firm Huntress told Gizmodo that three of its clients, who are MSPs and use VSA, had been affected by the attack and that, as a result, as many as 200 smaller businesses that rely on those MSPs had been hit with encryption.
“We are aware of four MSPs where all of the clients are affected — 3 US and one abroad. MSPs with over thousands of endpoints are being hit,” said John Hammond, a senior security researcher at Huntress. “When an MSP is compromised, we’ve seen proof that it has spread through the VSA into all the MSP’s customers.”
Hammond added that, “Based on everything we are seeing right now, we strongly believe this [is] REvil/Sodinikibi.”
REvil is a prominent cybercriminal gang that has used ransomware to go after high-profile targets, including Apple and Acer. It is also believed to be the gang that attacked meat supplier JBS, successfully extorting the large beef provider for $11 million.
America’s federal cybersecurity watchdog, the Cybersecurity and Infrastructure Security Agency, announced Friday that it was “taking action to understand and address the recent supply-chain ransomware attack against Kaseya VSA and the multiple managed service providers (MSPs) that employ VSA software.”
“CISA encourages organizations to review the Kaseya advisory and immediately follow their guidance to shutdown VSA servers,” the agency said.
UPDATE: Saturday, July 3, 2021, 1:10 p.m. EST.
So yeah, this attack is fucking huge.
By now, Kaseya has admitted that it’s not just one or two customers that have been affected by the hack—it’s “less than 40,” which is to say, it’s probably close to 40. When you consider how many of those customers may be MSPs and, in turn, may have hundreds of businesses relying on them, the number of affected parties is somewhat mind-boggling.
“Only a very small percentage of our customers were affected – currently estimated at fewer than 40 worldwide,” Kaseya’s CEO, Fred Voccola, said in an update Saturday. “We believe that we have identified the source of the vulnerability and are preparing a patch to mitigate it for our on-premises customers that will be tested thoroughly,” he added. “We will release that patch as quickly as possible to get our customers back up and running.” Voccola also said that the FBI is now investigating the incident.
Security firm Huntress, which works with some of the affected businesses and has been publicly tracking the attack, said via Reddit that the number of businesses that had been encrypted as a result of the attack had crested 1,000:
“We are tracking 20 MSPs where Kaseya VSA was used to encrypt over 1,000 business and are working in close collaboration with six of them. All of these VSA servers are on-premises and it seems likely that a vulnerability or feature was abused.”
In a follow-up sent to Gizmodo, Huntress provided the following:
“Based on a combination of the service providers reaching out to us for assistance along with the comments we’re seeing in the thread we are tracking on our reddit (/r/msp), it’s reasonable to think this could potentially be impacting thousands of small businesses.”
The attack is already derailing some of those businesses on a massive scale. In Sweden, a grocery chain known as Coop has apparently shut down 500 stores after a ransomware attack hit its MSP, Visma Esscom, Bleeping Computer reports. “One of our suppliers has been hit by an IT attack and therefore the cash registers do not work. We regret this and do everything to be able to open again soon,” the company apparently told patrons via Facebook.
The alleged culprit behind this whole mess, the ransomware gang REvil, appears to be setting different ransom prices for businesses depending on their size. The Washington Post reports that the hackers had been spotted sending out “two different ransom notes on Friday — demanding $50,000 from smaller companies and $5 million from larger ones.” The fact that REvil is ostensibly based in Russia could mean heightened tensions between the Biden administration and Vladimir Putin’s government, just after the two met during a conciliatory summit weeks ago.