A ransomware variant called NetWalker is doing surprisingly well, even in this economy. The malware, which takes computers hostage and asks for a Bitcoin ransom, raked in $25 million in the last five months, a solid haul for what amounts to a solid ransomware-as-a-service platform.
MacAfee explored the software in detail and found that business is (still) booming in the cryptojacking market.
“The total amount of extorted bitcoin that has been uncovered by tracing transactions to these NetWalker related addresses is 2795 BTC between 1 March 2020 and 27 July 2020. By using historic bitcoin to USD exchange rates, we estimate a total of 25 million USD was extorted with these NetWalker related transactions,” they write.
NetWalker is run by a group that has agreed not to target hospitals during the pandemic, making them a set of surprisingly charitable criminals.
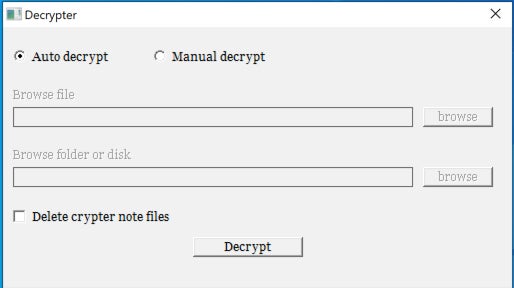
Interestingly, the ransomware is getting some solid upgrades. In its original version, the so-called NetWalker (or Mailto) software depended on emailed messages to unlock the user’s machines. Now, the system uses a pasted “security code” that the user must enter into a Tor-protected website. Once the payment goes through, the ransomware stores the crypto in SegWit addresses for “faster transaction time and lower transaction cost.”
“The NetWalker advertisement on the underground forum mentions instant and fully automatic payments around the time of this observed change. This makes us believe the ransomware actors were professionalizing their operation,” wrote MacAfee. Once you pay the ransom, the Tor site sends the victims a decryptor app that then decrypts all of the ransomed files.
Many high-profile ransomware attacks have stolen millions from corporate victims this quarter, making it a banner year for ransomware purveyors.