A new, Big-Tech-backed coalition is lobbying the Biden administration to more aggressively pursue the threat of ransomware. In a report sent to the White House this week, members of the new group—simply called the Ransomware Task Force—have asked the president and the U.S. intelligence community to prioritize the disruption of cybercriminal networks involved in the ongoing malware attacks against U.S. targets.
The 80-page report envisions a comprehensive strategy that brings public and private sectors together to more effectively target the underworld business model that supports ransomware, focusing on specific policies to bring down the infrastructure, payment systems, and individual criminal groups behind many of these attacks.
Launched by a Silicon Valley think-tank called the Institute of Security and Technology, the RTF has a diverse membership of more than 60 entities—ranging from people connected to large firms like Amazon and Microsoft to prominent cybersecurity companies such as FireEye, CrowdStrike, BlueVoyant, McAfee, and others. The group also includes staff from federal agencies like the Federal Bureau of Investigation, the Cybersecurity and Infrastructure Security Agency, and the Department of Homeland Security.
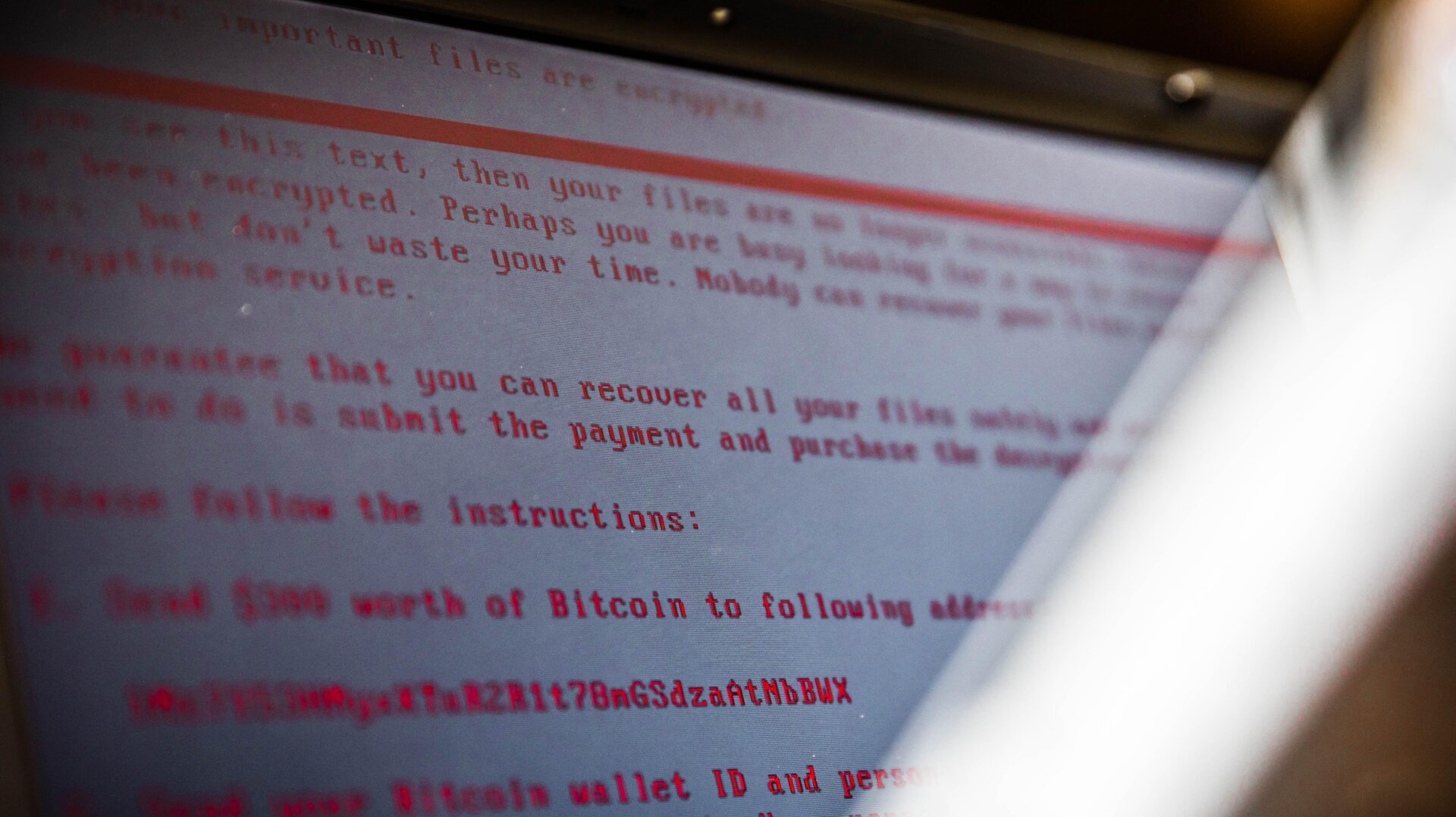
While ransomware has been around for decades, the last few years have seen a precipitous swell in U.S.-based activity—with state and local governments, schools, and businesses all feeling the brunt of such attacks. Recent incidents—like the leaking of sensitive internal police documents, or the widespread targeting of hospitals during the pandemic—also illustrate the increasingly aggressive and dangerous tactics that criminal groups are willing to carry out in order to seek payouts.
“Ransomware is not just financial extortion; it is a crime that transcends business, government, academic, and geographic boundaries,” the report states. “It is also a crime that funnels both private funds and tax dollars toward global criminal organizations. The proceeds stolen from victims may be financing illicit activities ranging from human trafficking to the development and proliferation of weapons of mass destruction.”
One of the more ambitious goals outlined in the report is to more effectively track the financial transactions connected to cyberattacks. “Ransomware attacks are profitable because ransom payments are made through the use of diverse cryptocurrencies, where payments are difficult to trace and can easily be laundered,” the report states. “The challenge for governments is to find new ways to get inside the ransomware payments process. It will be important to set measurable goals to assess progress toward this objective.” The report suggests developing relationships with blockchain analytic companies that can chart and map illicit activity on crypto platforms.
Unfortunately, it’s not totally clear whether the goals outlined in the report are actually that feasible or whether they will be pursued by policymakers, but it’s nevertheless a good sign that businesses and government are at least thinking about all this. For far too long, the U.S. has lacked even a basic strategy for how to address ransomware—and criminals, responsible for terribly destructive extortions, have mostly gotten off scot-free, as a very slim list of successful convictions demonstrates. The RTF’s report comes at a time when other groups, both public and private, are trying to figure out that strategy (the U.S. Justice Department recently launched its own task force dedicated to the issue), likely because—as a large data leak from the Illinois Attorney’s General’s Office today shows—this problem is getting ridiculous.