A new government study mostly lauding the Homeland Security Department’s handling of Americans’ personal information nevertheless detected “gaps” in the ways a few of its agencies have followed procedures designed to ward off security threats.
Analyzing data from six major DHS components, a Government Accountability Office (GAO) report released this month found certain IT systems managed by third-party contractors are “at increased risk of misuse and insufficient protection” due to a handful of key security practices reportedly unfollowed at DHS headquarters and at components such as the U.S. Coast Guard, the department’s lone military branch.
“While contractor personnel who operate systems and provide services to federal agencies can provide significant benefits,” GAO said, “they can also introduce risks to agency information and systems, such as the unauthorized access, use, disclosure, and modification of federal data.”
The report, requested by Sen. Maggie Hassan, chair of the Subcommittee on Emerging Threats and Spending Oversight, found that DHS components such as the Federal Emergency Management Agency (FEMA) and Immigration and Customs Enforcement (ICE) were largely following procedures designed to minimize risks to the unprecedented amounts of personally identifiable information collected by its contractors. (Personally identifiable information, or “PII,” can include a person’s name, date of birth, and Social Security number, along with information about their health, finances, or employment.)
Still, the GAO found that DHS headquarters, which allotted $7.6 billion for IT spending last year, had failed to provide essential privacy training to its contractors, and that the Coast Guard had no documentation proving it was capable of identifying and addressing gaps in its own security; a lapse that GAO says places contractor systems “at increased risk of unauthorized disclosure.”
What’s more, the congressional watchdog said it remained unconvinced that either the Coast Guard or the Transportation Security Administration (TSA)—the DHS component chiefly concerned with air travel—had suitable processes in place for evaluating whether and when to share personal data with new contractors for the first time; processes it describes as crucial to reducing the odds of abuse by contractors harnessing enormous volumes of personal data.
The GAO issued a total of seven recommendations, to which DHS fully agreed; however, DHS also asked that three of the recommendations be considered already in force. It offered no documentation, GAO said, that would support a decision to do so.
DHS did not respond to a request for comment before press time. A spokesperson for Sen. Hassan could not be immediately reached.
“Until DHS follows through on ensuring that components fully implement key privacy and remediation activities, PII is at increased risk of misuse and insufficient protection,” the GAO said, noting that DHS, among other agencies, have reported “increasing numbers of privacy incidents that have placed sensitive information at risk, with potentially serious impacts on federal operations, assets, and people.”
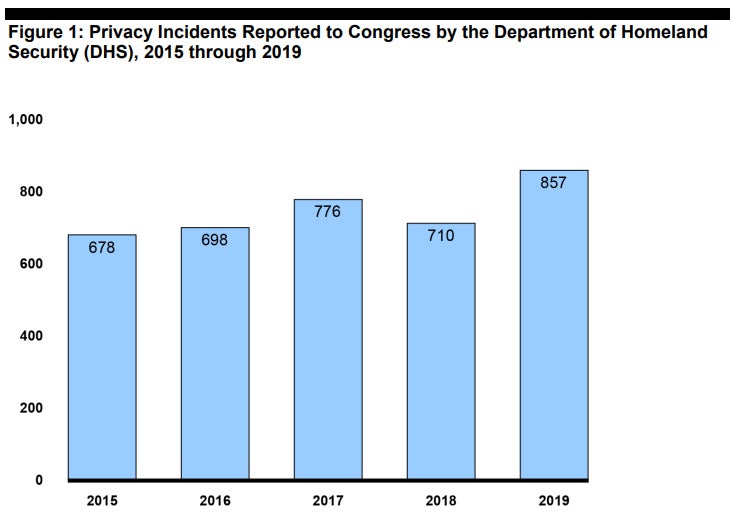
Data provided by DHS further revealed a 26% increase in so-called “privacy incidents” between 2015 and 2019, with an increase of more than 140 “incidents” in the final year. DHS and other agencies consider “privacy incidents” essentially any event involving the “loss of control, compromise, unauthorized disclosure, [or] unauthorized acquisition” of confidential personal data.
Inspector general audits in recent years have found failures at DHS to comply with basic cybersecurity standards. A 2019 audit, for example, assigned its security program the lowest possible grade; “effectively a letter grade of F,” noted a Senate report, published in August. Twenty-six “high vulnerabilities” were discovered at three DHS components, the report said, offering hackers a foothold in critical systems hosting highly sensitive data.






