One of the weirder stories from last year involved a gargantuan FBI honeypot operation designed to catch crooks all over the world. According to Motherboard, that operation had a bigger imprint in the U.S. than originally believed.
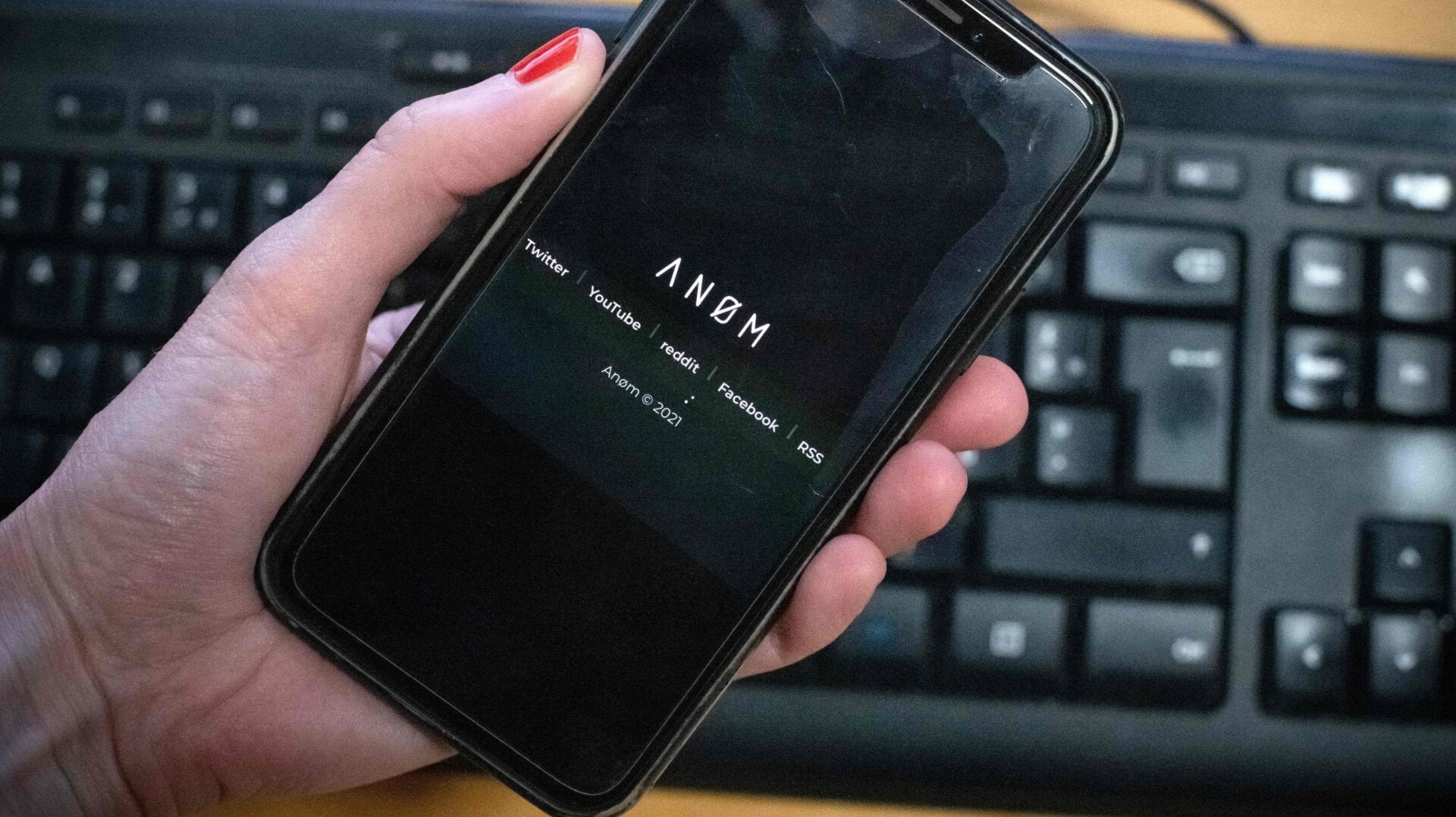
During “Operation Trojan Shield,” the feds used a secret relationship with an encrypted phone company, called Anom, which sold devices exclusively to career criminals looking for a secure way to communicate with one another. The product’s developer, who had previously been busted for drug trafficking, agreed to act as a high-level federal informant and for at least two years sold devices to criminals while also secretly cooperating with authorities. Meanwhile the FBI, along with its international partners, intercepted all of the communications, which allowed them to capture evidence of widespread criminal malfeasance on a global scale.
It made for one helluva weird story when the bureau finally revealed what it had been up to last June, and “Shield” led to the arrest of hundreds of alleged criminals in countries all around the world—many of which are accused of using the phones to facilitate drug trafficking and other forms of organized crime. The arrests continue to this day.
But there was one place that didn’t see any arrests, and that’s the United States. Due to legal issues, the FBI precluded surveillance of American users of the backdoored devices, apparently because they were concerned that the operation technically violated U.S. laws and threatened civil liberties—specifically the Fourth Amendment, which prohibits police search and seizure without a warrant. While a court filing revealed that at least 15 people located in the U.S. were known users of the trojanized devices, these individuals were said to have been geofenced by authorities conducting surveillance—meaning they were left out of the investigation.
That doesn’t mean that the Anom phones weren’t ultimately distributed in the U.S. Actually, a whole lot more were shipped to America than previously reported, according to Motherboard. The outlet recently reported that at least three different shipments of the phones made their way into the country. One of those shipments was made to a P.O. Box in New York in March 2020 and involved as many as 100 phones. Two other shipments, both of which were made to a drop point in San Diego, included a total of at least 10 devices.
It is still unclear how many phones in total were ultimately shipped to the U.S., and, once the phones were in the U.S., it’s unknown how many were actively used, whether they were picked up by the FBI, or if they were merely forwarded to other countries for use there, the outlet reports. As previously stated, we know that at least 15 of the phones were in use in the U.S. at some point, though details on who might have been using them or why are scant. Anom is said to have globally distributed around 12,000 of the phones, meaning that the U.S.’s portion—while potentially small—still made up a significant sliver. The phones were either distributed directly by Anom itself or by online distributors that the company had relationships with.
It’s an interesting detail about a fairly complex law enforcement operation—the full context of which is obviously still being uncovered.
Much has already been made about the legal sketchiness of “Trojan Shield.” Aside from the obvious civil liberties and privacy concerns with the FBI effectively “running” a backdoored phone company, the operation also inspired concerns that the op would ultimately undermine faith in the power of encryption—a useful tool not just for criminals but also for everyday people looking to maintain digital privacy.