While much attention has been paid to America’s National Security Agency over the last two years, reports now suggest that Canada’s Communications Security Establishment has been playing hardball too. A report by The Intercept claims that the agency’s “developed an arsenal of cyber weapons capable of stealing data and destroying adversaries’ infrastructure.”
In documents leaked from the National Security Agency by Edward Snowden, The Intercept has found claims by Canada’s CSE that it can perform “computer network exploitation” and “computer network attack” operations. In particular, it explains that it could “disable adversary infrastructure,” “control adversary infrastructure,” or “destroy adversary infrastructure”. The Intercept suggests that those capabilities could be used to attack infrastructure such as transportation, power or banking systems—a little like the Stuxnet attack.
The documents explain that the CSE is said to have “active computer network access and exploitation on a variety of foreign intelligence targets, including CT [counter terrorism], Middle East, North Africa, Europe, and Mexico.” Many of the tools it uses to carry out these operations are reportedly borrowed from the NSA.
It’s not the first news we’ve heard about the CSE aping the NSA. In January, leaked documents suggested that the Establishment monitors and stores details about downloads and uploads made via 102 different file-sharing websites. The documents explained that the Establishment finds 350 “interesting download events” each month—representing just 0.0001 per cent of the total collected data it grabs.
None of this is perhaps too surprising. But it does go to further demonstrate that the tactics employed by the NSA reach much further than just the United States. [The Intercept]
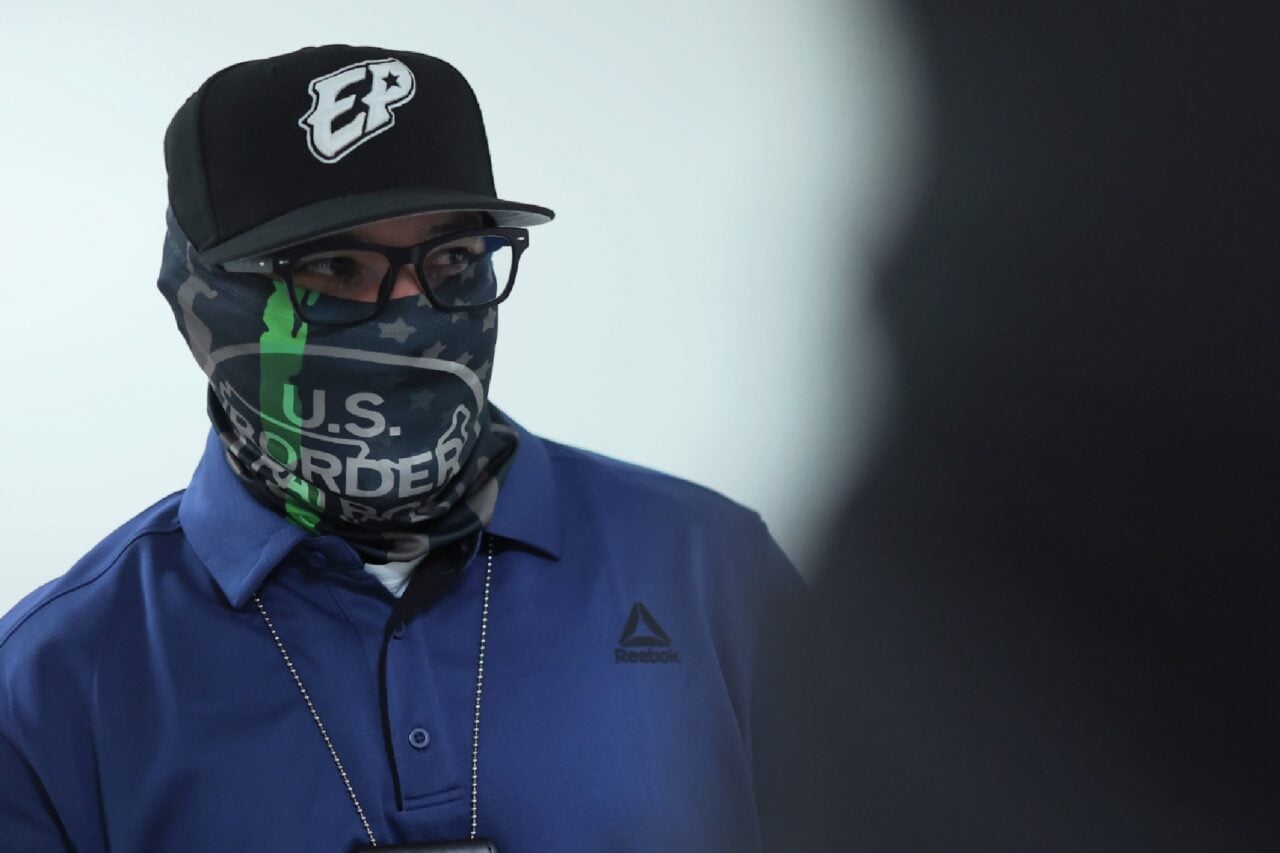
Image by Christopher Policarpio under Creative Commons license