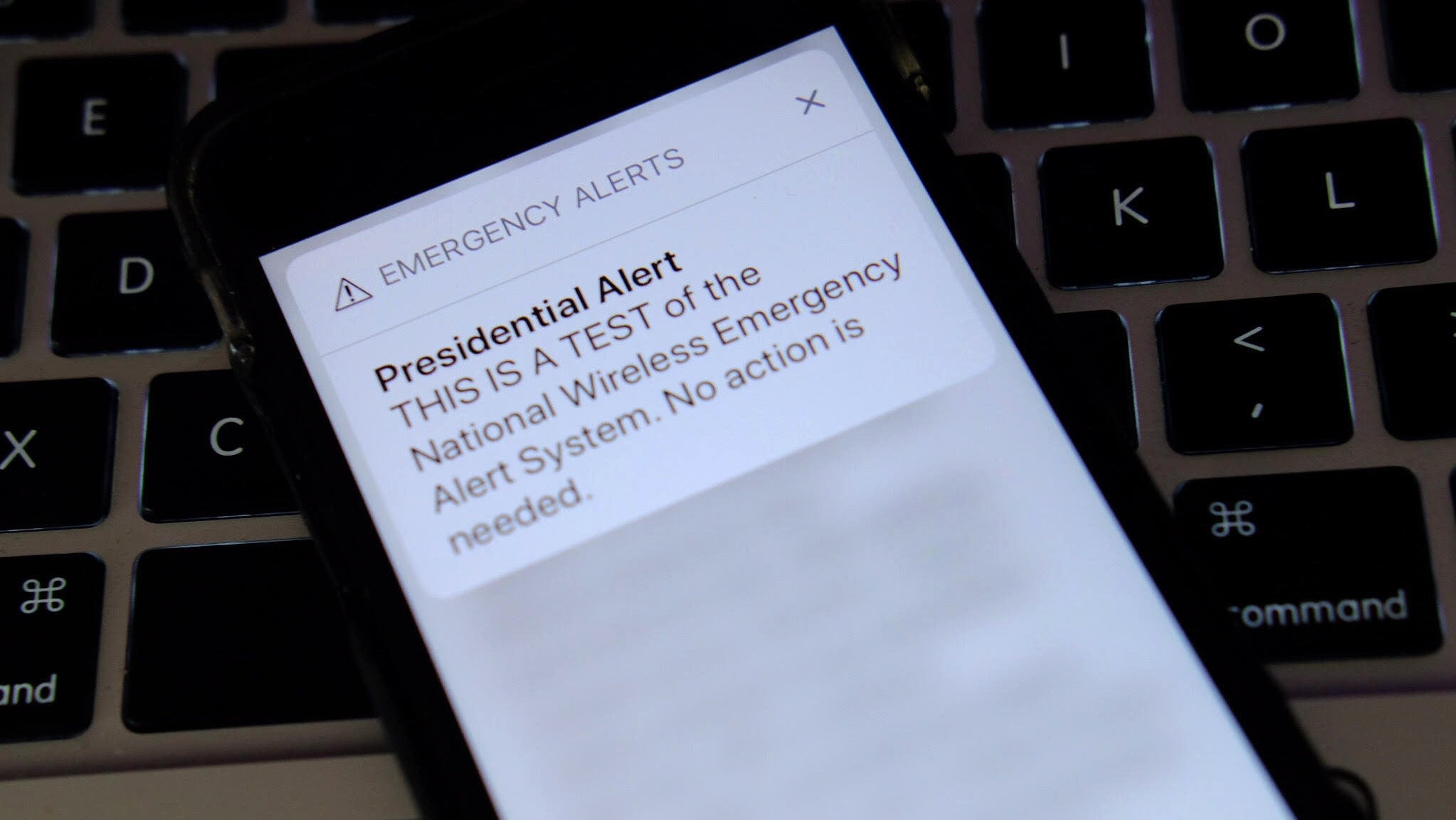
Researchers figured out a way to exploit the system that sends presidential emergency alerts to our phones, simulating their method on a 50,000 seat football stadium in Colorado with a 90 percent success rate.
Researchers at the University of Colorado Boulder published a paper this month that details how they were able to spoof attack the Wireless Emergency Alert (WEA) program, which can send out AMBER alerts, presidential alerts, and both extreme and severe threats to safety.
Emergency alerts are sent to every mobile device within range of the broadcasting cell tower. But the researchers note that a malicious cell tower channel is capable of fooling the system, and in turn sending out an inauthentic emergency alert to all devices within its range.
The researchers tested this LTE vulnerability by creating their own malicious cell tower channel using off-the-shelf hardware and open-source software to deploy their exploit, which in one instance was used in an experiment at Folsom Field at the University of Colorado Boulder.
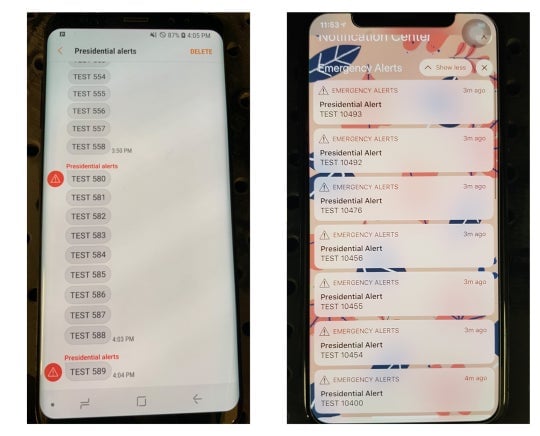
The researchers didn’t perform an actual attack on a live crowd at the stadium or on actual mobile devices, Eric Wustrow, a researcher on the paper, told Gizmodo in an email. The tests performed were instead done in isolated RF shield boxes, Wustrow said, “and our analysis of Folsom Field was a combination of empirically gathered data and simulation.” A screenshot from the paper below displays what these spoof attacks looked like on both a Samsung Galaxy S8 and an iPhone X.
“To the best of our knowledge, this is the first experimentally verified work that discloses the potential risk of CMAS spoofing,” the researchers wrote in the paper. CMAS refers to the standard WEA uses to send the emergency alerts. The researchers added that the LTE networks in countries like Europe, the US, and South Korea all have systems designed with principles similar to that of CMAS, “making them potential targets for the same attack.”
The researchers suggest some possible preventative measures that can be taken so that the spoofing attack they simulated won’t happen IRL. They recommend digital signatures to authenticate the messages as well as more securely authenticating the network and location of the network and the cell tower channel. “Fixing this problem will require a large collaborative effort between carriers, government stakeholders, and cell phone manufacturers,” the researchers wrote.
The nightmarish consequences of having such a system vulnerable to bad actors are not hard to imagine—tens of thousands of people in a crowded area receiving an ominous or straight up life-endangering warning at the same time is unlikely to end well. And bad actors aside, we’ve seen the very real traumatic effects of the failures of an emergency alert system—just last year, what can be boiled down to an atrocious communication mishap resulted in sending an imminent ballistic missile threat to residents of Hawaii.
While that wasn’t a security vulnerability issue, there are plenty of examples of how human error and technical flaws have plagued a system designed to inform people of emergencies and looming danger. If another weakness, such as a security flaw in the mobile communications standard the system is built upon, leads to even more false alarms, there are likely only two unsettling outcomes—a loss of faith in the system, or unnecessary and dangerous mass panic. And when senators are interested in injecting these very alerts into services like Netflix and Spotify, we better be sure as hell they can’t be screwed with.