A new report by a leading cybersecurity firm finds that healthcare organizations are becoming an increasingly attractive target for criminal hackers due to the premium that black markets place on private health information—and in particular, the credentials of physicians that can be used to facilitate health insurance fraud.
A key finding in the report, published Wednesday by Carbon Black, a Massachusetts-based security company, shows an astounding 83 percent of healthcare organizations have witnessed increased attacks on their networks. What’s more, two-thirds of the organizations surveyed say they’ve been targeted by ransomware. The same percentage noted such attacks are becoming progressively more sophisticated.
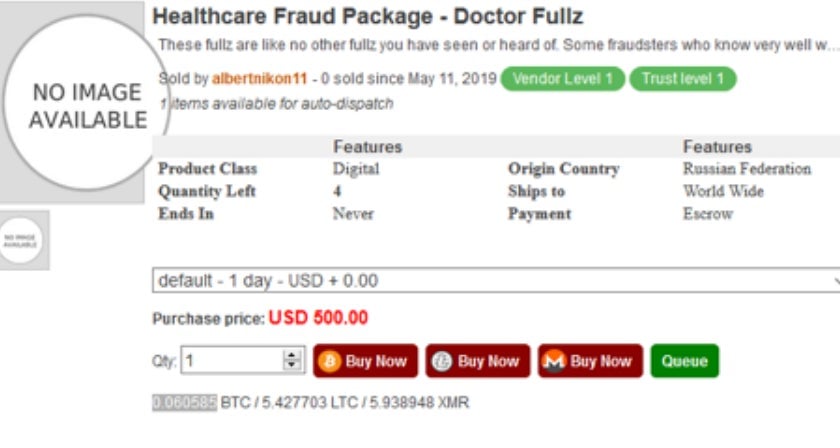
Analysis conducted by the firm, which serves some 5,300 clients worldwide, finds healthcare provider data is among the most valuable on darknet markets. This information, which may include medical doctor and Drug Enforcement Agency licenses, may allow actors to pose as physicians online. The information can be obtained for around $500 a pop.
Forgeries, meanwhile, are considerably cheaper, including prescription labels that sell between $10 and $20 per record. Even less expensive, health insurance login credentials can sell for as little as $3.25 each.
One listing, going for $500 on a darknet marketplace, is simply labeled, “Healthcare Fraud Package.”
“A hacker compromises the corporate network of a healthcare provider to find administrative paperwork that would support a forged doctor’s identity. The hacker then sells to a buyer or intermediary (who then sells to the buyer) for a high enough price to ensure a return on investment, but low enough to ensure multiple people buy the item,” the report states.
Once the stolen identity of a doctor is acquired, criminals can use it to submit claims to Medicare and other medical insurance providers for, among other types of treatment, high-end surgeries.
While there are considerable safeguards to overcome in acquiring drugs with fake prescription labels, that’s not the only reason people want them. They can be used, for instance, “as a defense against positive drug tests,” Carbon Black notes, as well as to help get prescription drugs through airport security.
One of the most common methods of acquiring physicians’ data is through the use of malicious Microsoft Office documents, the company says. “Ever since the Dridex malware campaign of 2011, malicious macros have become a staple ammunition for hackers who want to bypass legacy antivirus.”
Of the 83 percent of healthcare organizations who’ve witnessed an uptick in attacks over the past year, Carbon Black reports: “This number is not only congruent to industry data we’ve seen but also aligns with conversations we have with [chief information security officers] around the world.”
“Invariably, when we talk to these CISOs,” the report says, “almost all of them are saying that the number of relevant and actionable security alerts they are receiving continues to climb year over year.”






