It sounds like something out of an episode of Spooks: Researchers have discovered a way to use simple touch to decode the cryptography keys that are intended to secure your information. It’s as easy as gauging the electric potential coursing through your computer while it’s working.
In the MIT Technology Review today, we learn of a paper out of Tel Aviv University (title: Get Your Hands Off My Laptop) that details the process of measuring the ground electric potential in laptops. There are several ways to do this: You could, say, use a wire. But that’s not nearly as exciting as using your own hand—preferably sweaty!—and then “analyzing that signal using sophisticated software.”
Here’s how the authors explain the process:
This potential can be measured by a simple wire, non-invasively touching a conductive part of the laptop (such as the metal heatsink fins or shielding of USB, Ethernet, VGA, DisplayPort and HDMI ports), and connected to a suitable amplifier and digitizer. The chassis potential, thus measured, is affected by ongoing computation, and our attacks exploit this to extract RSA and ElGamal keys, within a few seconds.
According to the researchers, the hand method works “is especially effective in hot weather, since sweaty fingers offer lower electric resistance.”
Essentially, they’re taking advantage of the “noise” your computer makes while it’s processing this information, to figure out exactly when and how they should listen in. Which brings us to an important point: How to resist it. According to MIT, it’s “possible to avoid such attacks by adding random data to computations.” In other words, we’ll need to build codes on top of code. [MIT Technology Review]
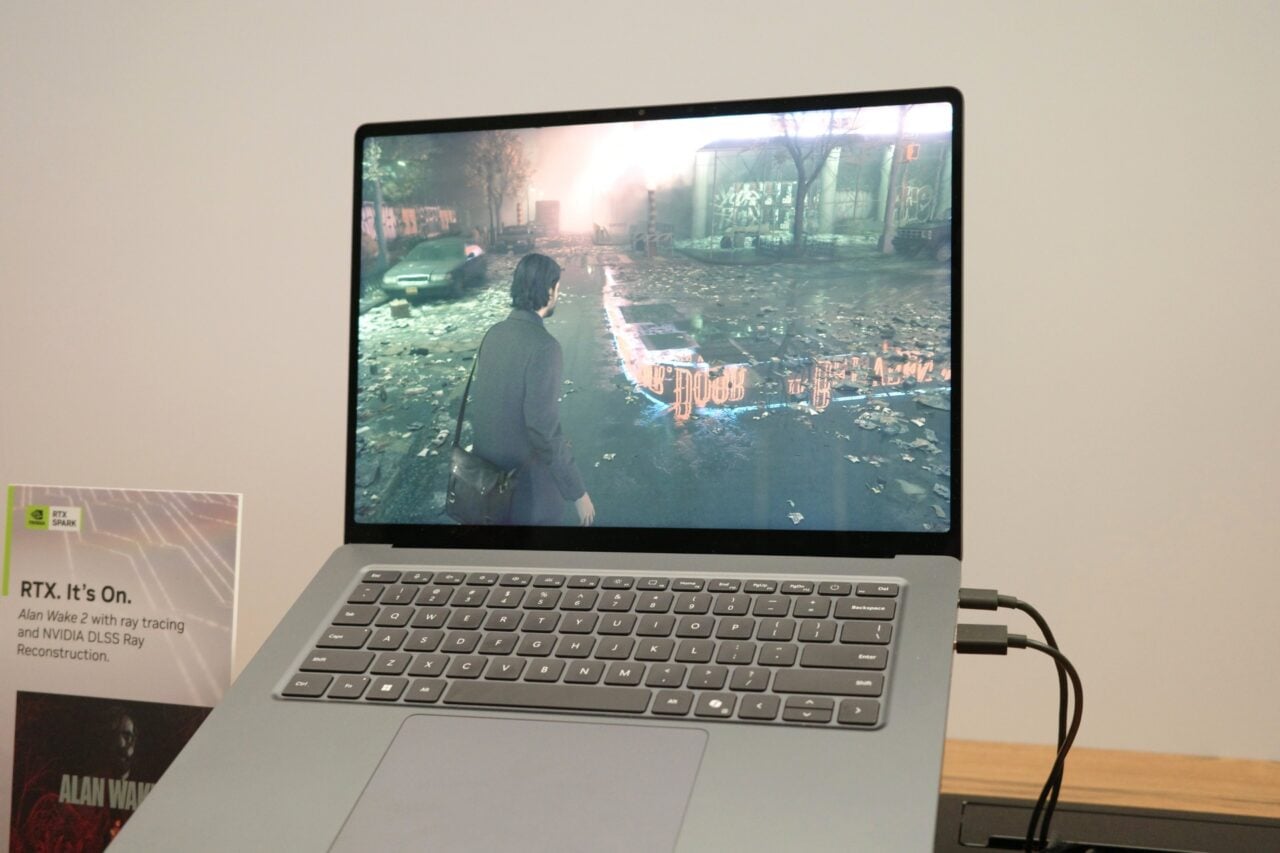
Image: Lasse Kristensen.