Kaseya, the cloud provider at the center of a gargantuan ransomware attack on hundreds of businesses, announced this week that it had some good news: Somehow, it had come into possession of a “universal decryptor” to unlock all of the data affected by the recent hack.
“We can confirm that Kaseya obtained the tool from a third party and have teams actively helping customers affected by the ransomware to restore their environments, with no reports of any problem or issues associated with the decryptor,” the company said in a statement put out Thursday.
The question remains, however: Where did that decryptor come from?
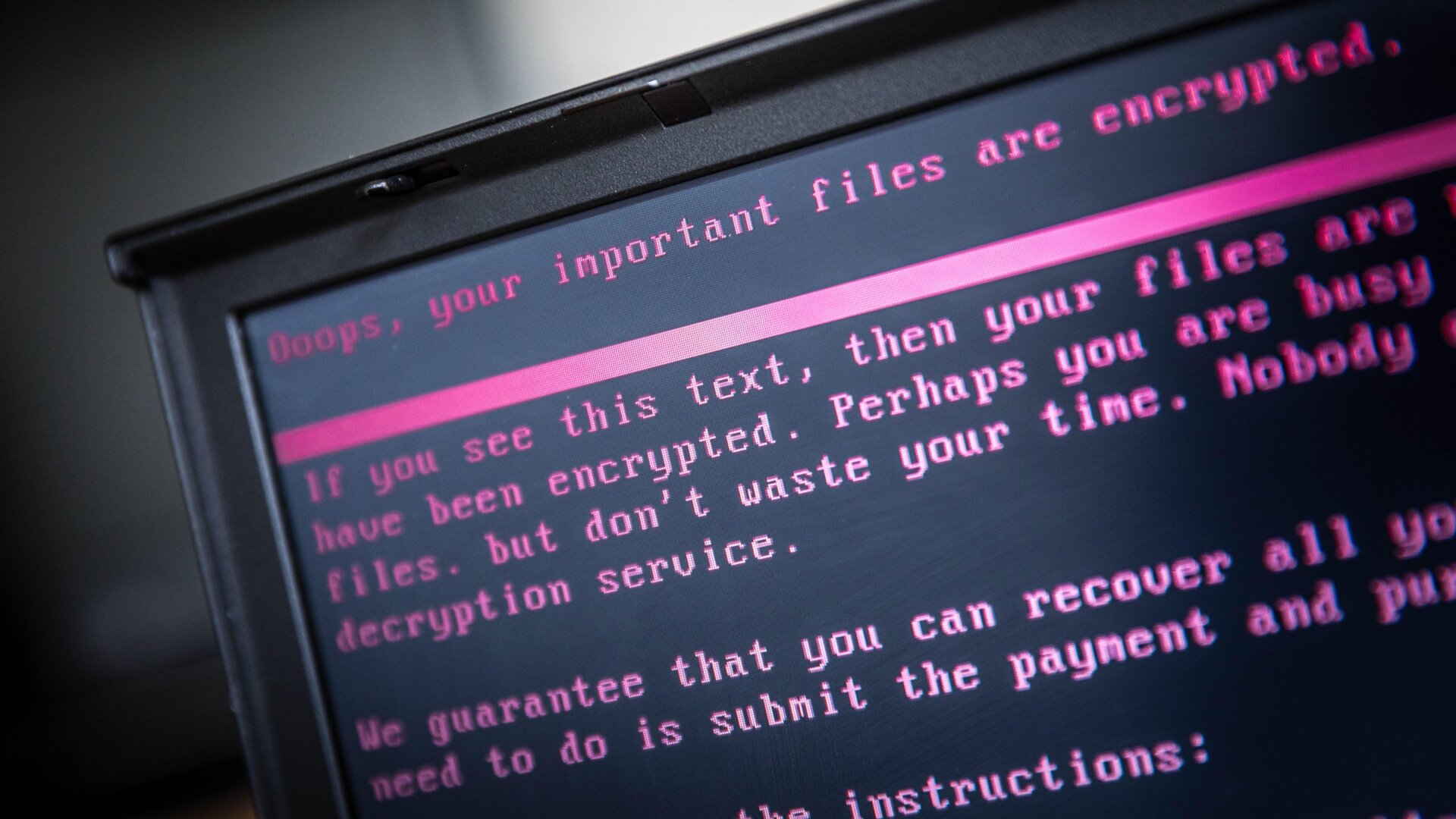
To review, the company was hit with ransomware this July 4 weekend and the Russian-speaking cybercriminal gang REvil subsequently claimed responsibility. The attack infected not just Kaseya but its client base, which, in turn, infected its client’s clients—ultimately affecting some 1,500 businesses worldwide.
REvil subsequently demanded $70 million in exchange for a universal decryption key to unlock all of the victims’ data.
However, in a surprising twist, the gang then proceeded to disappear from the web. Indeed, less than two weeks after REvil made its ransom demand, nearly all traces of the cybercriminal group vanished from the internet, including its website and payment portal.
Now, somehow, Kaseya says it has managed to get ahold of the universal decryption key, though it hasn’t explicitly said how that happened.
When asked by Gizmodo where the key came from, a Kaseya spokesperson reiterated that it had come from “a trusted third party.” When asked whether the company paid for the key, the spokesperson said that the company could not “comment to your question around payment.”
Even if the company had doled out the massive ransom, it’s not totally clear how or when an exchange would’ve occurred—since REvil has since “gone dark.” However, there are a couple theories floating around as to what may have happened.
Some experts have wondered whether the Russian government “might have seized the key from the criminals and handed it over through intermediaries,” The Guardian writes. This seems plausible, since we know that the Kaseya incident inspired significant political tensions between the White House and Kremlin. President Joe Biden reportedly had a curt conversation with Vladimir Putin not longer after the Kaseya attack, in which he asked the Russian leader to basically take responsibility for the cybercriminals operating within his nation’s borders.
Another hypothetical scenario could be that Kaseya actually paid the ransom quite early in the extortion process, thus exchanging the money for the key. That might explain why REvil has since disappeared. That is, if it accomplished what it set out to do, why not take the money and run?
All in all, it’s another somewhat mysterious resolution to a large-scale ransomware attack—a trend that seems to be increasingly common. A similarly vague climax occurred in early June, when the FBI announced that it had somehow managed to track and seize a majority of the ransom payment paid to the gang DarkSide after its attack on Colonial Pipeline. The feds never disclosed their methods and, similar to the situation involving REvil, DarkSide proceeded to “go dark” around the same time that the FBI seized its money.