Conference calls aren’t going away, and now it seems like it might not be a bad idea to close the blinds if you’re discussing sensitive matters. Researchers from Ben-Gurion University have come up with a way to listen in on a speaker from afar by just monitoring the subtle changes in brightness of its power status LED.
The Glowworm Attack, as the discovery is called, follows similar research from the university published in 2020 that found an electro-optical sensor paired with a telescope was able to decipher the sounds in a room. Sound waves bounced off a hanging light bulb create nearly imperceptible changes in the lighting in the room. With the Glowworm Attack, the same technology that made Lamphone possible is repurposed to remotely eavesdrop on sounds in a room again, but using a completely different approach that many speaker makers apparently never even considered.
The effect is completely imperceptible to both the human eye and the limited frame rate of a high-resolution video camera. As an electromagnet increases and decreases its power to make a speaker cone move back and forth to create audible sound waves, the ever-changing power draw also slightly increases and decreases the amount of power reaching a speaker’s power status LED, causing it to dim and brighten. Even in a dark room your eyes won’t see it happening, but there’s enough of a change that an electro-optical sensor, which simply converts light into an electrical signal, can detect it.
Pairing the sensor with a telescope allowed the security researchers at Ben-Gurion University to successfully capture and decipher sounds being played by a speaker at distances of up to 35 meters, or close to 115 feet. The results aren’t crystal clear (you can hear the remote recordings the researchers made on Ben Nassi’s website), and the noise increases the farther away from the speaker the capture device is used, but with some intelligent audio processing, the results can undoubtedly be improved.
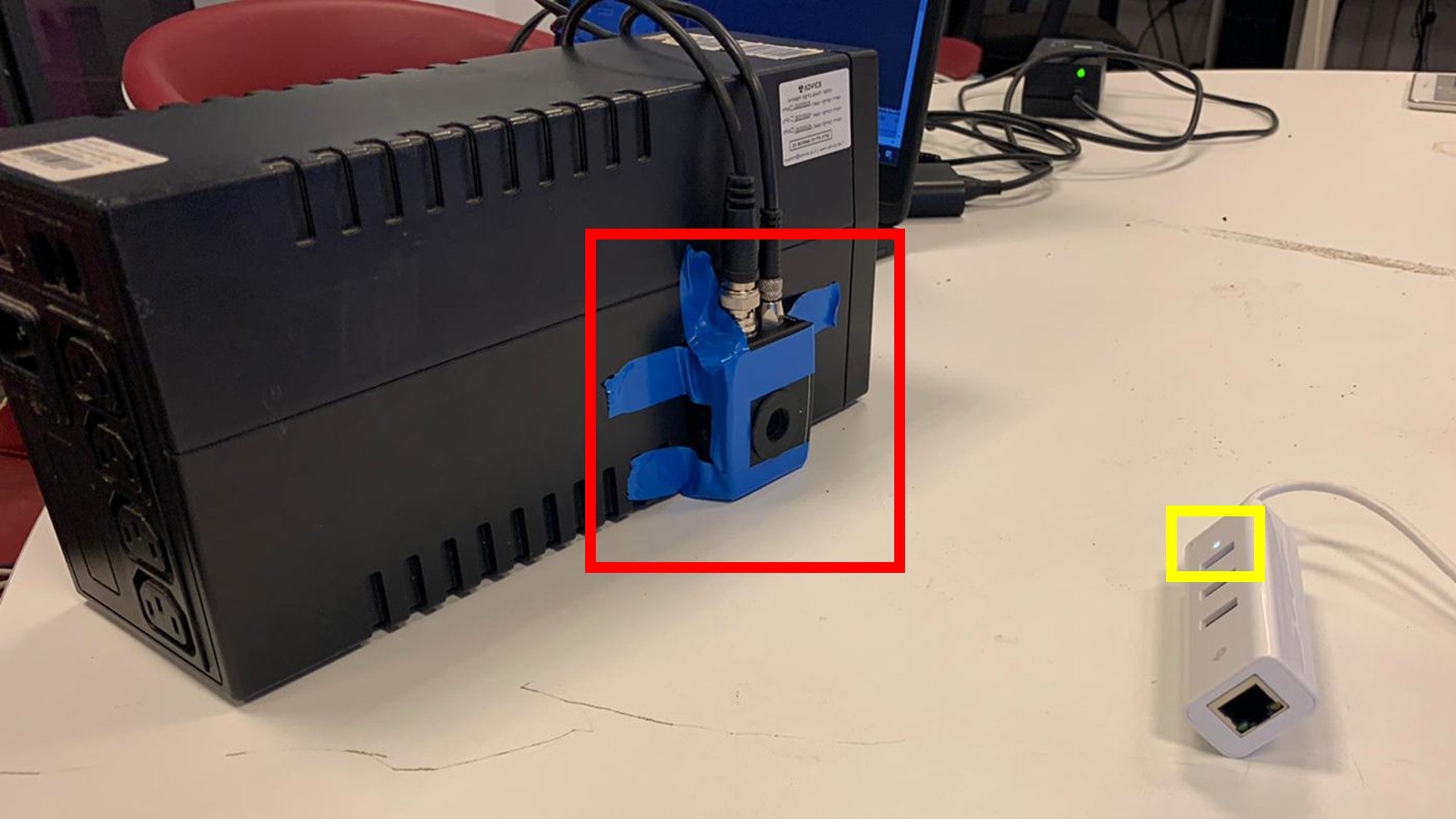
The researchers tested the Glowworm Attack on speakers from several different manufacturers, including the Google Home Mini and Google Nest Audio smart speakers, as well as offerings from brands like Logitech, Sony, Creative, and JBL (who have all been informed of the attack.) It’s not limited to just speaker hardware, however. The researchers were also able to successfully capture audio by remotely analyzing the LEDs on USB hubs that desktop speakers were plugged into, as well as connected devices like the Raspberry Pi.
Thankfully, there are plenty of ways to foil the Glowworm Attack, with the easiest being a strategically placed piece of opaque tape preventing the power status LED from being seen. On the manufacturer side, the solution might be a little harder, but as Hackaday suggests, introducing some randomized power noise to the LED while the speaker is operating should properly obfuscate what it’s revealing to eavesdroppers nearby.