Google is still failing to catch malicious apps from being listed on its app store, but it seems that some developers that have been cited aren’t even being kicked off the platform. Security software company Malwarebytes reported Tuesday that four apps listed by developer Mobile apps Group contain a well-known malware used to steal users’ information. As of the time of reporting, all four apps are still listed on Google Play Store.
Worse still, Malwarebytes wrote that the developer in question has been found deploying malware in its apps before, yet they’re still able to list their apps on Google’s main app store.
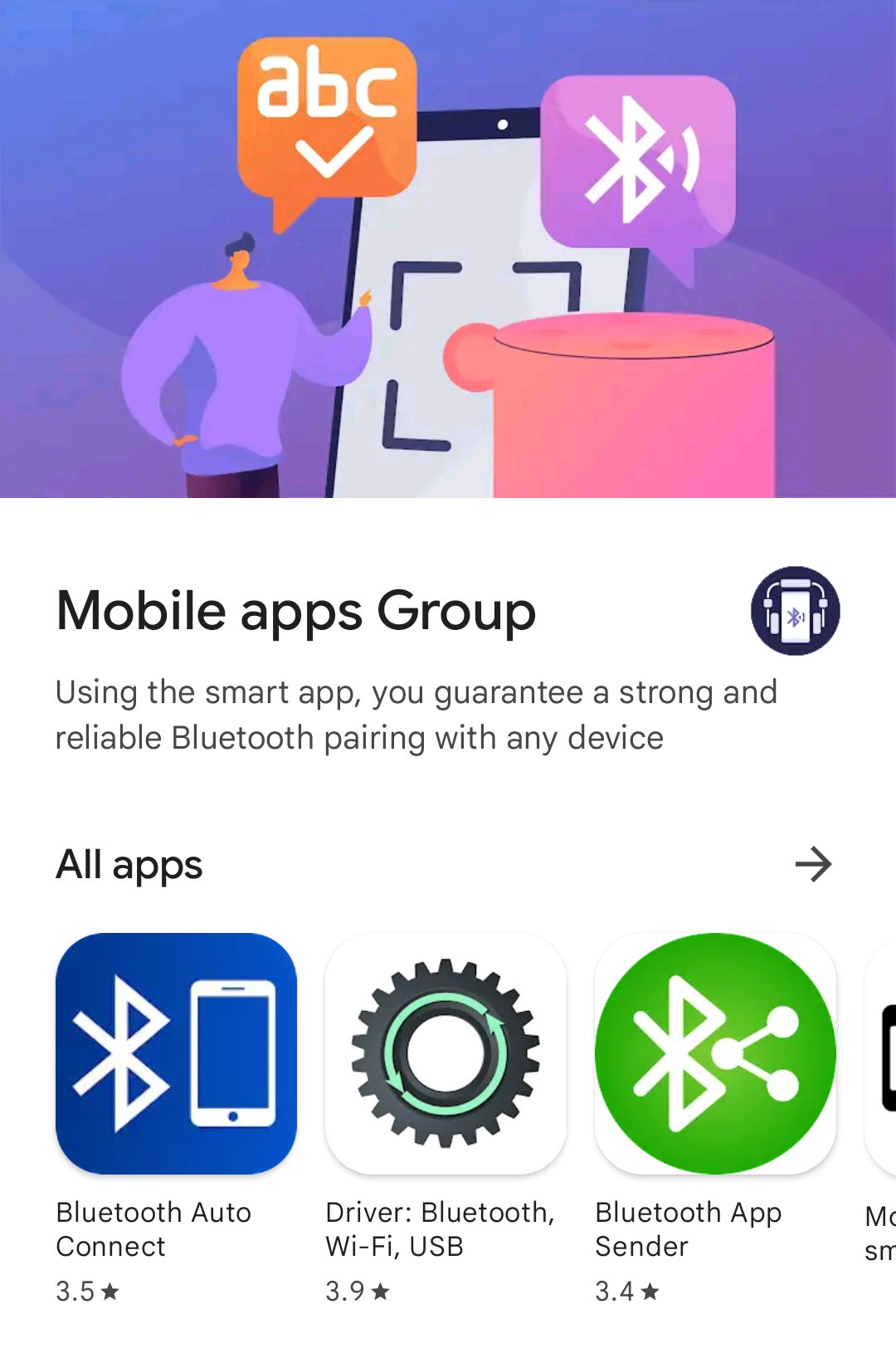
The apps are listed by the company Mobile apps Group, whose listing on Play Store includes the tagline “Using the smart app, you guarantee a strong and reliable Bluetooth pairing with any device.” The apps include:
Bluetooth Auto Connect
Driver: Bluetooth Wi-Fi, USB
Bluetooth App Sender
Mobile transfer: smart switch
Nathan Collier, a malware intelligence analyst for Malwarebytes, wrote that when users first install Bluetooth Auto Connect, there’s a several-day delay before it starts opening phishing sites in Chrome. These sites run in the background even if a device is locked and open automatically when users unlock their phones. These phishing sites reportedly include porn sites that lead to phishing pages or other sites that spam users with messages that they’ve been hacked and need to perform an update.
Mobile apps group has been cited twice in the past for listing malware-infected apps, according to Collier. Other cybersecurity researchers have bloggedabout an earlier version of Bluetooth Auto Connect. Two days after that blog and subsequent delisting, the developers released a 3.0 version on Google Play, which means those malicious devs did not even receive a probation period. The devs released the current 5.7 version of the app last December, meaning that the malware has potentially remained for close to a year.
Google did not immediately respond to Gizmodo’s request for comment. Google has a stated policy against any app that includes malware of any type, and the system claims it warns users if it detects a violation of its malware policy.
Collier wrote that first log entry from the malware called Android/Trojan.HiddenAds.TBGTHB is recorded a few hours after he installed the app, though the time before it installs varies between the different apps.
There have been loads of other high-profile malicious app scandals on Google Play, including one Muslim prayer app that was harvesting users’ phone numbers. Last year, Google booted nine other apps from its store after researchers found they used malware to steal users’ Facebook logins.
Delaying malware infiltration is a common way that bad actors get around app store filters, Collier wrote. It remains unclear why Google was unable to detect these apps, but another recent report from cybersecurity company Bitdefender noted there were 35 other malicious apps being listed on Play Store that have racked up over 2 million downloads in total. That August report noted that once these apps are installed they rename themselves and change their app icon in order to confuse users and avoid detection. An even earlier report from July by Dr. Web noted a few dozen other malware-infected apps were modifications to known malware.
Google Play Protect is the company’s built-in malware defense program, and according to its own page it scans over 100 billion apps on Google Play every day. But researchers have previously noted that it so routinely fails at catching malware, ranking last among other security apps in 2021 tests by IT security researchers at AV Test.






