“Oh don’t worry,” your uncle said when you were shopping for a new computer. “Macs are virtually virus proof.” Your uncle was wrong.
A team of white hat hackers just announced the development of the world’s first firmware worm that’s vicious enough to break through Apple’s legendary security. The so-called Thunderstrike 2 attack can be delivered through a phishing email or a peripheral device like a USB stick or even an ethernet adaptor. The worm then targets a machine’s option ROM or lives in the option ROM of peripherals so that even computers not connected to a network can be infected. It also can’t be removed from the firmware unless you open up the box and manually re-flash the chip. Oh, and the worm can’t be detected by any existing security software, so good luck with that.
“Let’s say you’re running a uranium refining centrifuge plant and you don’t have it connected to any networks, but people bring laptops into it and perhaps they share Ethernet adapters or external SSDs to bring data in and out,” Xeno Kovah, one of the firmware security consultants that developed the worm, told Wired. “Those SSDs have option ROMs that could potentially carry this sort of infection. Perhaps because it’s a secure environment they don’t use WiFi, so they have Ethernet adapters. Those adapters also have option ROMs that can carry this malicious firm.”
If you’re running a uranium centrifuge plant, you definitely don’t want any type of worm in your computer system, especially one that could spread without being detected and destroy without fear of destruction. Kovah likened Thunderstrike 2 to the infamous Stuxnet worm that infected Iran’s uranium enrichment facilities a few years ago.
Don’t freak out just yet, though. Thunderstrike 2 is very apparently named after the original Thunderstrike virus, which was shown off at the Chaos Computer Congressin Germany earlier this year. Much like the sequel, Thunderstrike targeted Mac firmware and could not be detected. However, the original virus required physical access to the machine via Thunderbolt peripherals, while Thunderstike 2 can also be delivered remotely. Apple acknowledged Thunderstrike over six months ago and addressed the vulnerabilities, so there’s much hope that it will patch the new vulnerabilities that Thunderstrike 2 targets, too.
All that said, the really scary thing isn’t imagining how your computer might fall victim to a vicious undetectable worm called Thunderstrike. That’s a known threat now, one that will almost definitely be addressed. The horrifying thing is imagining what other kinds of worms governments are developing—the naughty bastard offspring of Stuxnet that stand to end the world with a single keystroke. We know that the NSA is working hard on firmware hacking, and you can be sure that China’s army of hackers is interested.
They’re probably not going to present their findings at Black Hat and Def Con, like the creators of Thunderstrike 2 are. Only Thor can save us now.
[Wired]
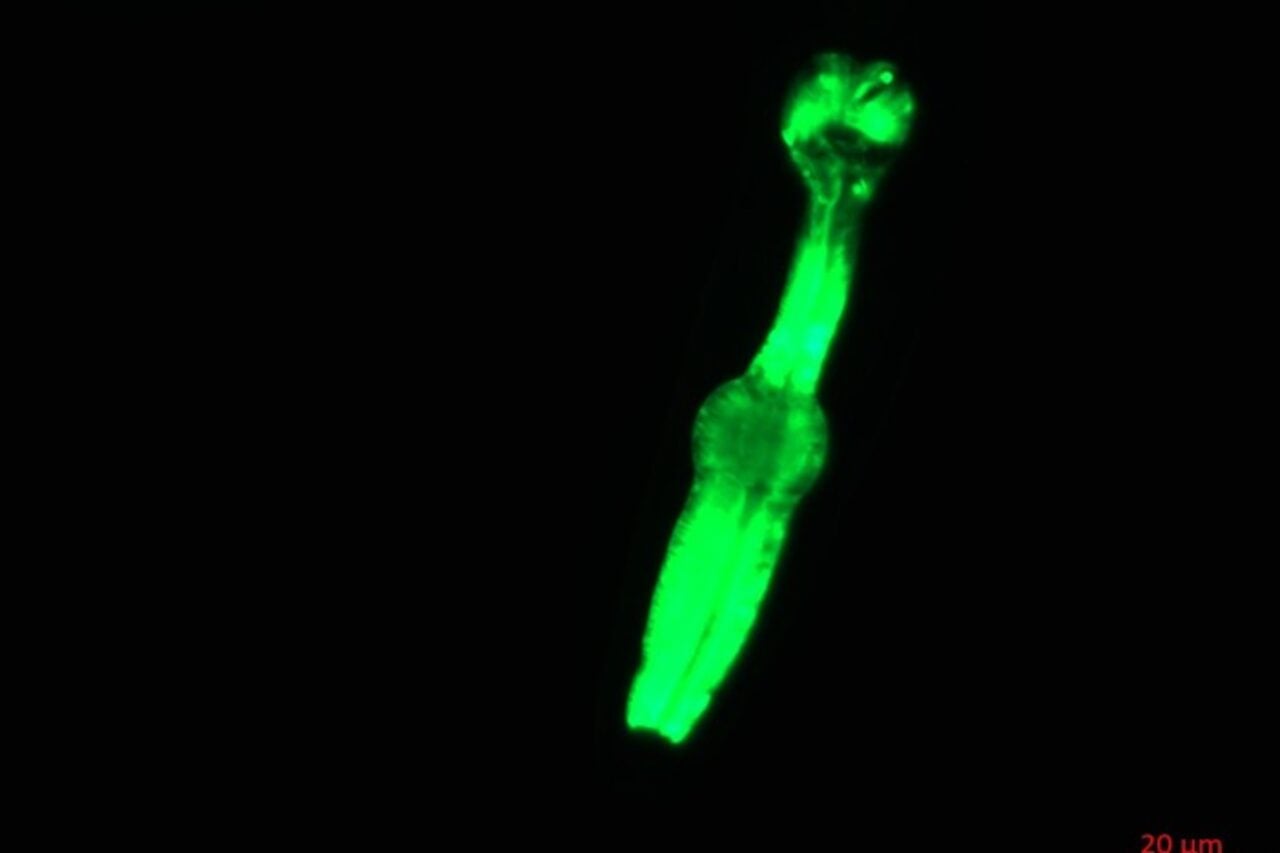
Image via Flickr / Tobias Bischoff